Hackers Breach Government and Military Servers by Exploiting cPanel Vulnerability
Cyber Espionage Unmasked: How a cPanel Vulnerability Led to Government and Military Breaches
A disturbing new report details a sophisticated cyberattack that leveraged a critical cPanel authentication bypass to infiltrate sensitive government and military infrastructure in Southeast Asia. This campaign, meticulously executed by an advanced persistent threat (APT) actor, highlights the relentless ingenuity of cyber adversaries and the crucial need for robust security postures, even on widely used platforms.
The Anatomy of an Advanced Campaign
The attack began with the rapid exploitation of CVE-2026-41940, a severe cPanel authentication bypass vulnerability with a critical CVSS score of 9.8. This initial breach provided the attackers with a critical foothold. From there, they demonstrated significant operational sophistication by deploying a custom zero-day exploit chain specifically designed to target an Indonesian defense-sector portal. This multi-stage approach allowed the threat actors to pivot deep within the networks, ultimately culminating in the exfiltration of over 4GB of sensitive Chinese railway documents.
This incident underscores that even seemingly isolated vulnerabilities can be weaponized as part of a larger, highly coordinated offensive. The combination of exploiting a known, critical vulnerability with a custom zero-day showcases a high level of expertise and resource allocation from the perpetrators.
Understanding CVE-2026-41940: A Critical cPanel Flaw
CVE-2026-41940 represents a severe authentication bypass vulnerability within cPanel, a popular web hosting control panel. An authentication bypass allows an attacker to circumvent security measures designed to verify a user’s identity, granting unauthorized access to the system. In this specific case, the flaw’s critical CVSS score of 9.8 indicates that it is easily exploitable and can lead to complete compromise of the affected system, often without requiring complex attack techniques or elevated privileges. For system administrators and hosting providers, such vulnerabilities are particularly concerning due to cPanel’s widespread use across millions of websites and servers.
Escalation and Data Exfiltration
After gaining initial access via the cPanel vulnerability, the threat actors did not stop there. They exploited a previously unknown zero-day vulnerability targeting an Indonesian defense-sector portal. This strategic move allowed them to expand their lateral movement capabilities within the compromised networks. The ultimate objective was clearly intelligence gathering, as evidenced by the successful exfiltration of over 4GB of sensitive Chinese railway documents. The type of data stolen suggests a nation-state sponsored or highly capable espionage group with specific intelligence requirements and a long-term strategic objective.
Remediation Actions for cPanel and Network Security
Protecting against such sophisticated attacks requires comprehensive and proactive security measures. For cPanel users and administrators, immediate action is paramount.
- Patch Immediately: Ensure that all cPanel installations are running the absolute latest security patches. Monitor cPanel’s official announcements for updates related to CVE-2026-41940 and apply them without delay.
- Principle of Least Privilege: Implement strict access controls for cPanel users and system administrators. Grant only the necessary permissions required for specific roles.
- Multi-Factor Authentication (MFA): Enforce MFA for all cPanel logins. This adds a crucial layer of security, making it significantly harder for attackers to gain access even if they compromise credentials.
- Regular Security Audits: Conduct frequent security audits and vulnerability assessments of cPanel servers and connected infrastructure.
- Network Segmentation: Isolate critical systems and sensitive data from less secure parts of the network to limit lateral movement in the event of a breach.
- Intrusion Detection/Prevention Systems (IDS/IPS): Deploy and properly configure IDS/IPS solutions to detect and block suspicious activity and known exploit patterns.
- Zero-Trust Architecture: Adopt a zero-trust model, assuming no user or device is trustworthy by default, regardless of whether it is inside or outside the network perimeter.
- Employee Training: Educate staff, particularly those with administrative access, about phishing attacks, social engineering, and the importance of strong, unique passwords.
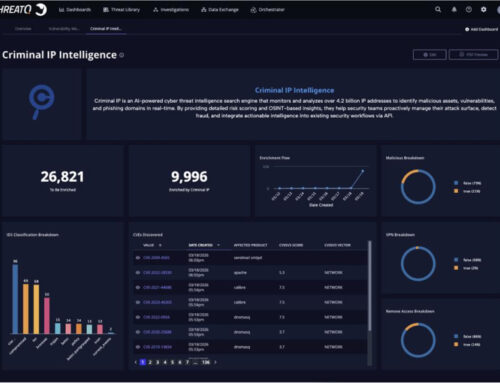
Tools for Detection and Mitigation
Leveraging appropriate tools is essential for maintaining a strong security posture. Here are some relevant tools:
| Tool Name | Purpose | Link |
|---|---|---|
| Tenable Nessus | Comprehensive vulnerability scanning and management | https://www.tenable.com/products/nessus |
| OpenVAS | Open-source vulnerability scanner | http://www.openvas.org/ |
| Snort | Network Intrusion Detection System (NIDS) | https://www.snort.org/ |
| ModSecurity | Web Application Firewall (WAF) for cPanel environments | https://www.modsecurity.org/ |
| MFA Solutions (e.g., Google Authenticator, YubiKey) | Enhance login security with multi-factor authentication | https://authenticator.withgoogle.com/ |
Key Takeaways from the cPanel Exploitation
This incident serves as a stark reminder of several critical cybersecurity lessons:
Firstly, the exploitation of widespread platforms like cPanel presents attractive targets for sophisticated adversaries. Organisations must prioritize patching and securing all components of their IT infrastructure, however ubiquitous.
Secondly, the combination of a known vulnerability (CVE-2026-41940) with zero-day exploits demonstrates a high level of threat actor capability. Defense strategies must evolve beyond simply addressing public vulnerabilities to include robust threat hunting and incident response frameworks.
Finally, the targeting of government and military entities, alongside the theft of sensitive intelligence, underscores the persistent threat of cyber espionage. Continuous vigilance, thorough security audits, and adherence to best practices are not optional but fundamental requirements for protecting national security and sensitive data.