How to Protect Against DDoS Attacks
How to Protect Against DDoS Attack Mitigation: Prevent Distributed Denial of Service
In today’s digital landscape, Distributed Denial of Service (DDoS) attacks pose a significant threat to online services and network infrastructure. Understanding how these attacks work and implementing effective DDoS mitigation strategies is crucial for maintaining business continuity and protecting against service disruptions. This article explores the nature of DDoS attacks, common attack types, and practical steps to prevent and mitigate these cyber threats.
Understanding DDoS Attacks
Understanding DDoS attacks is crucial for effective DDoS protection. A DDoS attack is a type of cyberattack where multiple compromised systems are used to target a single system, such as a server, website, or network, causing a denial of service for legitimate users. These attacks aim to overwhelm the target with malicious traffic, making it unavailable.
What is a DDoS Attack?
A DDoS attack, short for Distributed Denial of Service attack, is a malicious attempt to disrupt the normal traffic of a server, service, or network by overwhelming it with a flood of incoming traffic from multiple sources. The attacks aim to make a web application or online resource unavailable to legitimate users, causing significant downtime. It’s a serious DDoS threat that requires robust DDoS defense mechanisms.
Common Types of DDoS Attacks
Here are some common types of DDoS attacks, each targeting different weaknesses in server resources and network infrastructure:
- Volumetric attacks aim to overwhelm bandwidth by flooding it with massive amounts of traffic.
- Application layer attacks target specific vulnerabilities found in web applications.
Protocol attacks exploit weaknesses in network protocols to disrupt service and can be stopped by DDoS mitigation techniques.
How DDoS Attacks Affect Services
DDoS attacks can severely impact online services, potentially causing significant negative consequences. These consequences often include:
- Service disruptions, making it impossible for legitimate users to access online resources.
- Financial losses, reputational damage, and a decrease in customer trust.
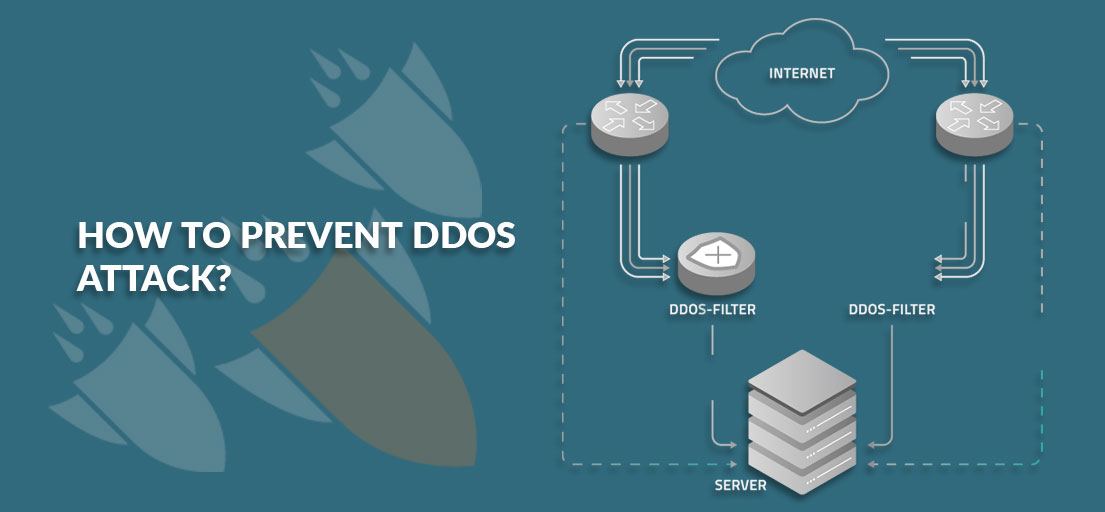
How to Prevent DDoS Attacks
Best Practices for DDoS Protection
To effectively prevent DDoS attacks, organizations must adopt best practices for DDoS protection. This involves implementing robust DDoS defense mechanisms such as intrusion detection systems and intrusion prevention systems. Organizations should also regularly update their security protocols to defend against DDoS attacks and patch vulnerabilities that attackers might exploit. Strong DDoS attack prevention measures are essential for maintaining online service availability.
Implementing a Web Application Firewall
Implementing a web application firewall (WAF) is a crucial step in preventing DDoS attacks. A WAF analyzes incoming network traffic to a web application and filters out malicious traffic, including application-layer attacks. By examining HTTP traffic, a web application firewall can identify and block many types of DDoS attacks, thus providing an essential layer of DDoS protection for web applications and online services.
Utilizing IP Address Management
Utilizing IP address management is another effective strategy to mitigate DDoS attacks targeting web servers.. Effective IP address management involves monitoring and analyzing IP addresses accessing your network to identify suspicious traffic patterns. IP address reputation can be used to block malicious IP addresses and prevent them from participating in distributed denial-of-service attacks. Effective IP management is a critical component of DDoS mitigation strategies.
Mitigation Strategies for DDoS Attacks
Volumetric Attack Mitigation Techniques
Volumetric attacks are a common type of DDoS attack, aimed at overwhelming bandwidth with massive amounts of traffic. To mitigate volumetric DDoS attacks, organizations can use techniques such as traffic shaping and filtering. These techniques help manage the incoming attack traffic and prioritize legitimate users, preventing the server from being overwhelmed and maintaining service availability during a flood attack.
Layered Approach to Mitigation
A layered approach to DDoS mitigation involves using multiple security measures to defend against DDoS attacks, ensuring comprehensive DDoS protection and the resilience of online services. This includes implementing firewalls, intrusion detection systems, and content delivery networks (CDNs). By combining different DDoS protection methods, organizations can create a robust DDoS defense strategy that mitigates various types of DDoS attacks, ensuring comprehensive DDoS protection and the resilience of online services.
Application Layer Attack Defense
To defend against application-layer attacks, organizations can implement web application firewalls and intrusion detection systems to analyze incoming web application traffic and filter out malicious requests, preventing service disruptions. Application layer attacks target specific vulnerabilities in web applications to cause a denial of service for legitimate users. To defend against application-layer attacks, organizations can implement web application firewalls and intrusion detection systems to analyze incoming web application traffic and filter out malicious requests. This helps mitigate these attacks and ensures the continued availability of online services, preventing service disruptions.
Detecting DDoS Attacks
Signs of a DDoS Attack
Early detection is paramount for successful DDoS mitigation. There are several telltale signs to watch out for, including:
- A sudden surge in network traffic
- A server becoming unresponsive or a specific web application slowing down significantly
Analyzing traffic patterns can reveal malicious traffic from multiple IP addresses, indicating a distributed denial-of-service attempt against DNS servers. Keep a watchful eye on your online services.
Tools for Detection
Several types of DDoS attacks target different aspects of network security. Mitigation tools are crucial for effective DDoS prevention and maintaining server resources. are available to detect a DDoS attack. Network monitoring software can analyze incoming traffic and identify unusual spikes or patterns. Intrusion detection systems can flag malicious activity targeting your server. A web application firewall can also help detect Application layer attacks are a specific type of attack that targets web server vulnerabilities. by analyzing web application traffic and identifying suspicious requests.
Responding to a Detected Attack
Once you implement a robust DDoS prevention strategy, your network will be more resilient to attacks. detect a DDoS attack, immediate action is necessary to mitigate its impact. Activate your DDoS defense plan, which may include traffic filtering, rate limiting, and using a Cloud-based DDoS protection is increasingly popular for safeguarding against various types of denial-of-service attacks. service. Contact your internet service provider (ISP) to coordinate efforts to block malicious traffic. Act quickly to protect your online services and Mitigation tools are essential to effectively mitigate attacks and minimize downtime..
Stopping a DDoS Attack
Immediate Response Actions
To stop a DDoS attack, immediate response actions are critical. Start by enabling your DDoS mitigation plan, which may involve activating a web application firewall to filter malicious traffic. Implement rate limiting to control the volume of incoming traffic. Engage your DDoS protection services provider to activate their DDoS defense mechanisms. Don’t let the attacks overwhelm your network infrastructure.
Long-term Defense Solutions
Long-term DDoS defense solutions are essential to prevent DDoS attacks. These solutions include investing in robust DDoS protection infrastructure, such as a web application firewall and intrusion detection systems. Regularly update your security protocols and patch vulnerabilities to defend against DDoS attacks. Implement proactive monitoring to mitigate DDoS attacks before they cause significant service disruptions.
Collaborating with ISPs for Better Defense
Collaborating with ISPs is a crucial part of a comprehensive DDoS prevention strategy.. ISPs can help identify and block distributed denial-of-service attacks before they impact server resources. malicious traffic before it reaches your network infrastructure. They can also provide valuable insights into legitimate traffic patterns to help identify potential threats. attack traffic patterns and assist in developing effective DDoS mitigation strategies. By working together, you can significantly enhance your ability to mitigate denial-of-service attacks. mitigate attacks.
How can I detect a DDoS attack and what signs of an attack indicate a distributed denial-of-service?
Detect a DDoS attack by monitoring for common signs of an attack: sudden traffic spikes from many IPs, unexpected geographic distribution, repeated connection attempts, and degraded server response times leading to service interruption. Network equipment and logs will often show anomalous patterns across the network and indicate a DDoS attack when normal baselines are exceeded. Early indicators include increased latency, packet loss, and spikes in specific attack vectors such as SYN floods or UDP storms; these potential DDoS signals help trigger a ddos response plan without disrupting legitimate users.
What mitigation solutions and ddos mitigation tools should be used to mitigate and defend against DDoS attacks?
To mitigate and defend against DDoS attacks, deploy layered mitigation solutions: on-premise network equipment (firewalls, load balancers, scrubbing appliances) together with cloud-based DDoS protection solutions and traffic scrubbing services. DDoS mitigation tools include rate limiting, IP/geo-blocking, behavior-based anomaly detection, and automated filtering that work across the network to prevent downtime. Combining mitigation efforts with a tested ddos response plan ensures uninterrupted service and reduces the impact of sophisticated DDoS attacks.
Which protection tools and security strategy help prevent DDoS attacks without disrupting normal traffic?
A sound security strategy to help prevent DDoS attacks uses protection tools such as CDN caching, Web Application Firewalls (WAF), and elastic autoscaling to absorb surges while preserving service level for legitimate users. Implement traffic shaping, challenge-response for suspicious sessions, and upstream cooperation with ISPs and DDoS protection providers. Regularly update mitigation solutions and rehearse incident playbooks so that when an attack is detected the response minimizes downtime and defends against attacks that may exploit multiple attack vectors.
How do distributed denial-of-service attacks target DNS servers and servers, and how can businesses protect your business?
Distributed denial-of-service attacks often target DNS servers and application servers to overwhelm name resolution and origin infrastructure, leading to service outages. Protection includes distributing DNS across redundant providers, using anycast routing, and isolating critical services behind DDoS protection services to prevent downtime. For businesses, adopt a layered ddos protection solution, maintain capacity planning, and include mitigation efforts in your security strategy to ensure uninterrupted service and reduce the risk from sophisticated DDoS campaigns that may include multiple attack types.