Critical 18-Year-Old NGINX Vulnerability Enables Remote Code Execution Attacks – PoC Released
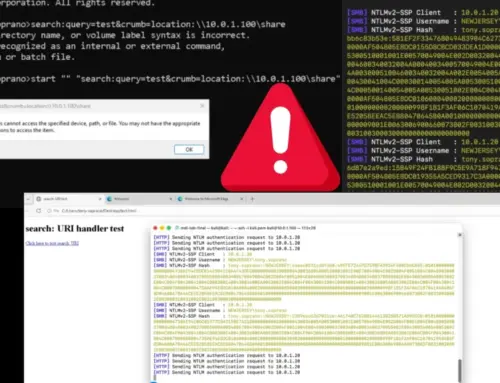
A silent threat, nearly two decades old, has just roared into the spotlight, shaking the foundations of web infrastructure globally. A critical heap buffer overflow vulnerability, quietly residing in NGINX’s source code since 2008, has been publicly unveiled. What makes this revelation particularly alarming? It comes complete with a working proof-of-concept (PoC) exploit, demonstrating unauthenticated Remote Code Execution (RCE) capabilities against one of the internet’s most widely deployed web servers. This isn’t just another vulnerability; it’s a stark reminder that even mature, long-standing software can harbor significant, undiscovered risks. For organizations relying on NGINX, immediate attention is paramount.
The NGINX RCE Vulnerability: A Deep Dive
Dubbed CVE-2026-42945, this critical flaw has been assigned a CVSS score of 9.2, signaling its severe impact. The vulnerability lives within NGINX’s ngx_http_rewrite_module, the very engine responsible for powering URL rewriting and redirection functionalities. Essentially, this module, a core component for many web applications, contains a weakness that, when exploited, can allow an attacker to execute malicious code on the server without needing any prior authentication.
A heap buffer overflow occurs when a program attempts to write data beyond the allocated buffer in dynamic memory (the heap). In the context of NGINX, this could allow an attacker to overwrite adjacent memory locations, potentially corrupting data, altering program flow, or, in the worst-case scenario, achieving full RCE. The fact that a PoC has been released means the window for exploitation has dramatically shortened, placing all unpatched NGINX instances at immediate risk.
Impact of Unauthenticated Remote Code Execution
The implications of unauthenticated RCE are profound. An attacker can:
- Gain complete control: Execute arbitrary commands on the compromised server.
- Data Exfiltration: Access, steal, or delete sensitive data stored on the server or connected systems.
- System Compromise: Install backdoors, create new user accounts, or pivot to other systems within the network.
- Web Defacement: Alter the content of websites hosted on the NGINX server.
- Denial of Service: Disrupt service availability by crashing the server or exhausting resources.
Given NGINX’s widespread use as a web server, reverse proxy, load balancer, and HTTP cache, a successful exploit could lead to widespread disruption and significant data breaches across various industries.
Remediation Actions: Securing Your NGINX Servers
Urgent action is required to mitigate the risk posed by CVE-2026-42945. Organizations running NGINX should prioritize the following steps:
- Immediate Patching: Monitor official NGINX channels for security announcements and apply patches as soon as they become available. This is the most crucial step.
- Configuration Review: Even before patches are out, review NGINX configurations, particularly those using the
ngx_http_rewrite_module. While this may not fully prevent exploitation, understanding your exposure is vital. - Least Privilege Principle: Ensure that the NGINX process runs with the absolute minimum necessary privileges. This limits the damage an attacker can inflict even if RCE is achieved.
- Network Segmentation: Isolate NGINX servers from critical internal networks as much as possible. This can help contain the spread of an attack.
- Web Application Firewall (WAF): Implement a WAF to inspect and filter incoming requests. A well-configured WAF might detect and block exploit attempts, though it should not be considered a silver bullet against novel RCEs.
- Regular Audits: Conduct regular security audits and penetration tests of your NGINX deployments to identify and address potential weaknesses proactively.
- Stay Informed: Subscribe to NGINX security advisories and trusted cybersecurity news sources for ongoing updates regarding this vulnerability and others.
Tools for Detection and Mitigation
While an official patch is the primary defense, several tools can assist in detecting vulnerabilities, scanning for misconfigurations, and layering defenses.
| Tool Name | Purpose | Link |
|---|---|---|
| Nessus | Vulnerability Scanning & Assessment | https://www.tenable.com/products/nessus |
| OpenVAS | Open Source Vulnerability Scanner | https://www.openvas.org/ |
| ModSecurity | Web Application Firewall (WAF) | https://www.modsecurity.org/ |
| NGINX App Protect | Advanced WAF for NGINX | https://www.nginx.com/products/nginx-app-protect/ |
| Qualys VMDR | Vulnerability Management, Detection, and Response | https://www.qualys.com/apps/vmdr/ |
What This Means for the Cybersecurity Landscape
This disclosure serves as a sobering reminder that sophisticated vulnerabilities can persist in fundamental software components for extended periods. The unearthing of a nearly two-decade-old critical RCE in NGINX underscores the continuous need for rigorous security research, code auditing, and a proactive approach to vulnerability management. For developers, it emphasizes the importance of secure coding practices and continuous security testing throughout the software development lifecycle. For organizations, it reinforces the mandate to maintain up-to-date systems, implement multi-layered security controls, and have robust incident response plans in place.
The immediate threat from CVE-2026-42945 is undeniable, demanding prompt attention from all NGINX users. Staying vigilant, applying patches swiftly, and understanding the core mechanisms of such attacks are key to safeguarding digital assets in an increasingly complex threat landscape.