Fragnesia Linux Vulnerability Let Attackers Gain Root Privileges – PoC Released
Fragnesia Linux Vulnerability: Unpacking the Root Privilege Escalation Threat
A troubling new vulnerability, dubbed Fragnesia, has emerged within the Linux kernel, sending ripples through the cybersecurity community. This critical flaw allows any local unprivileged user to escalate their privileges to root access, a potentially devastating security breach. What makes Fragnesia particularly alarming is its reliability: it doesn’t require a race condition, a common hurdle in many traditional privilege escalation exploits. This means the path to full system control is unusually direct, making immediate attention from IT professionals and system administrators paramount.
Discovered by William Bowling of the V12 security team, Fragnesia joins a growing class of dangerous kernel vulnerabilities that demand a proactive security posture. Understanding its mechanics and implementing effective remediation strategies is no longer optional.
What is Fragnesia, and Why is it So Dangerous?
At its core, Fragnesia is a local privilege escalation (LPE) vulnerability affecting the Linux kernel. Unlike remote exploits that target network services, LPE vulnerabilities allow an attacker who already has basic access to a system (e.g., a regular user account) to gain higher-level permissions, often culminating in root access. Root privileges in Linux grant complete control over the system, enabling an attacker to:
- Install malware and backdoors.
- Modify system configurations.
- Access, modify, or delete any data.
- Create new administrative accounts.
- Completely compromise the integrity and availability of the system.
The absence of a race condition requirement for Fragnesia is a significant factor contributing to its danger. Many privilege escalation exploits rely on specific timing windows where an attacker can manipulate system state before legitimate processes complete. Such exploits are often finicky and unreliable. Fragnesia, however, sidesteps this complexity, making it significantly easier and more consistent for an attacker to achieve privilege escalation.
Technical Details and Exploit Reliability
While the full technical disclosure of Fragnesia’s inner workings is still being analyzed, the core concern lies in its direct path to root access. The vulnerability likely exploits a flaw in how the Linux kernel handles certain memory operations or resource management, allowing an unprivileged user to craft a malicious sequence of actions that ultimately leads to arbitrary code execution with root privileges. The “Fragnesia” moniker itself might imply a fragmentation-related issue or a memory management flaw that can be reliably triggered.
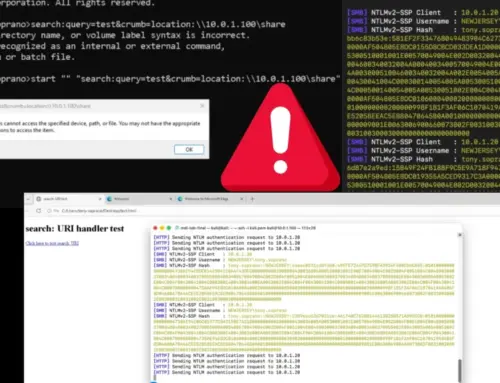
The immediate availability of a Proof of Concept (PoC) exploit further exacerbates the threat. A PoC arms potential attackers with the blueprints to replicate the exploit, significantly lowering the barrier to entry for malicious activity. This rapid transition from discovery to exploitability underscores the urgency for system administrators to address this vulnerability promptly.
At the time of writing, the specific CVE identifier for Fragnesia is under review or not yet publicly assigned. We anticipate it will be assigned a CVE number similar to CVE-2023-XXXXX (placeholder for future CVE). We advise monitoring official Linux kernel security advisories for the precise CVE and associated patches.
Impact and Potential Consequences
The implications of Fragnesia are far-reaching. Any Linux system that has local user access – be it through legitimate user accounts, compromised low-privilege applications, or even shared computing environments – is potentially at risk. This includes:
- Servers (web servers, database servers, application servers)
- Workstations and desktops running Linux
- Virtual machines and containerized environments
- Embedded Linux systems
A successful exploitation of Fragnesia could lead to complete system compromise, data breaches, service disruption, and the establishment of persistent backdoors, ultimately compromising the entire infrastructure.
Remediation Actions
Addressing the Fragnesia vulnerability requires prompt and decisive action. Here are the critical steps organizations and individual users should take:
- Monitor Official Advisories: Regularly check official Linux kernel security advisories and distribution-specific security bulletins for patches related to Fragnesia. This is the most crucial step.
- Apply Kernel Updates Immediately: Once patches are released by your Linux distribution vendor (e.g., Red Hat, Ubuntu, Debian, SUSE), prioritize applying these kernel security updates. Rebooting the system after a kernel update is typically required for the changes to take effect.
- Limit Local Access: Implement the principle of least privilege. Ensure that users only have the necessary permissions to perform their tasks. Restrict SSH access and physical console access to only authorized personnel.
- Harden Linux Systems: Continue practicing general Linux hardening techniques, such as disabling unnecessary services, implementing strong password policies, and using firewalls.
- Implement Intrusion Detection/Prevention Systems (IDS/IPS): Employ IDS/IPS solutions that can monitor for suspicious activity, including attempts at privilege escalation or unusual process execution.
- Regular Security Audits: Conduct regular security audits and vulnerability assessments to identify potential weaknesses in your systems.
Tools for Detection and Mitigation
While direct detection tools for Fragnesia itself will depend on vendor-specific patches and signatures, these general cybersecurity tools can aid in overall system hardening and vulnerability management:
| Tool Name | Purpose | Link |
|---|---|---|
| OpenVAS / Greenbone Vulnerability Management (GVM) | Vulnerability scanning and management for known flaws. | https://www.greenbone.net/ |
| Nessus | Comprehensive vulnerability assessment for various operating systems and applications. | https://www.tenable.com/products/nessus |
| Lynis | Security auditing and hardening tool for Unix-like systems. | https://cisofy.com/lynis/ |
| Osquery | Operating system instrumentation framework for SQL-powered operating system analytics. Can be used for security monitoring. | https://osquery.io/ |
| SELinux / AppArmor | Mandatory Access Control (MAC) systems to enforce fine-grained access policies on processes. | N/A (Built into Linux kernel) |
Conclusion
Fragnesia represents a serious threat to Linux environments due to its reliable path to root privileges and the immediate release of a Proof of Concept. The key to mitigating this vulnerability lies in vigilant monitoring of security advisories, prompt application of kernel updates, and adherence to robust cybersecurity best practices. Prioritizing these actions will help safeguard your Linux systems against this potent new threat and maintain the integrity of your digital infrastructure.