No Blind Spots: How Top MSSPs Prevent Incidents withLive Threat Visibility
Every digital defense strategy faces a critical challenge: moments of invisibility. It’s in these blind spots that incidents germinate – a network connection missed by the SIEM, a newly registered domain evading detection rules, or an Indicator of Compromise (IOC) active for days before any threat intelligence feed flags it. These initial oversights are often the genesis of significant client damage. While analytical prowess and advanced tools are undeniably valuable, the top-performing Managed Security Service Providers (MSSPs) recognize that true incident prevention stems from a more fundamental capability: live threat visibility.
This isn’t about simply adding more tools or hiring more analysts; it’s about achieving omnipresence within a client’s digital ecosystem. It means seeing threats as they emerge, before they escalate into full-blown attacks. This article explores how leading MSSPs achieve this crucial visibility, transforming their operations from reactive response to proactive prevention.
The Pervasiveness of Invisibility: Why Blind Spots Exist
The modern threat landscape is dynamic and multifaceted. Traditional security approaches often struggle to keep pace. Several factors contribute to the “moments of invisibility” that plague even well-resourced organizations:
- Fragmented Security Stacks: Disparate security tools, each with its own logs and alerts, often create siloes of information. Integrating these effectively for a unified view is a persistent challenge.
- Evolving Threat Tactics: Adversaries constantly innovate, employing new evasion techniques, polymorphic malware, and zero-day exploits. Security solutions designed for yesterday’s threats can easily miss today’s sophisticated attacks.
- Data Overload and Alert Fatigue: Security Information and Event Management (SIEM) systems can generate an overwhelming volume of alerts. Analysts, stretched thin, can become desensitized to warnings, leading to legitimate threats being overlooked.
- Lack of Contextual Understanding: Raw logs and isolated alerts rarely provide the full picture. Understanding the context – who, what, when, where, and why – is critical for discerning genuine threats from benign anomalies.
- Delayed Threat Intelligence Integration: New IOCs and threat signatures are constantly emerging. Delays in integrating this intelligence into active detection rules mean a window of vulnerability exists before systems are updated.
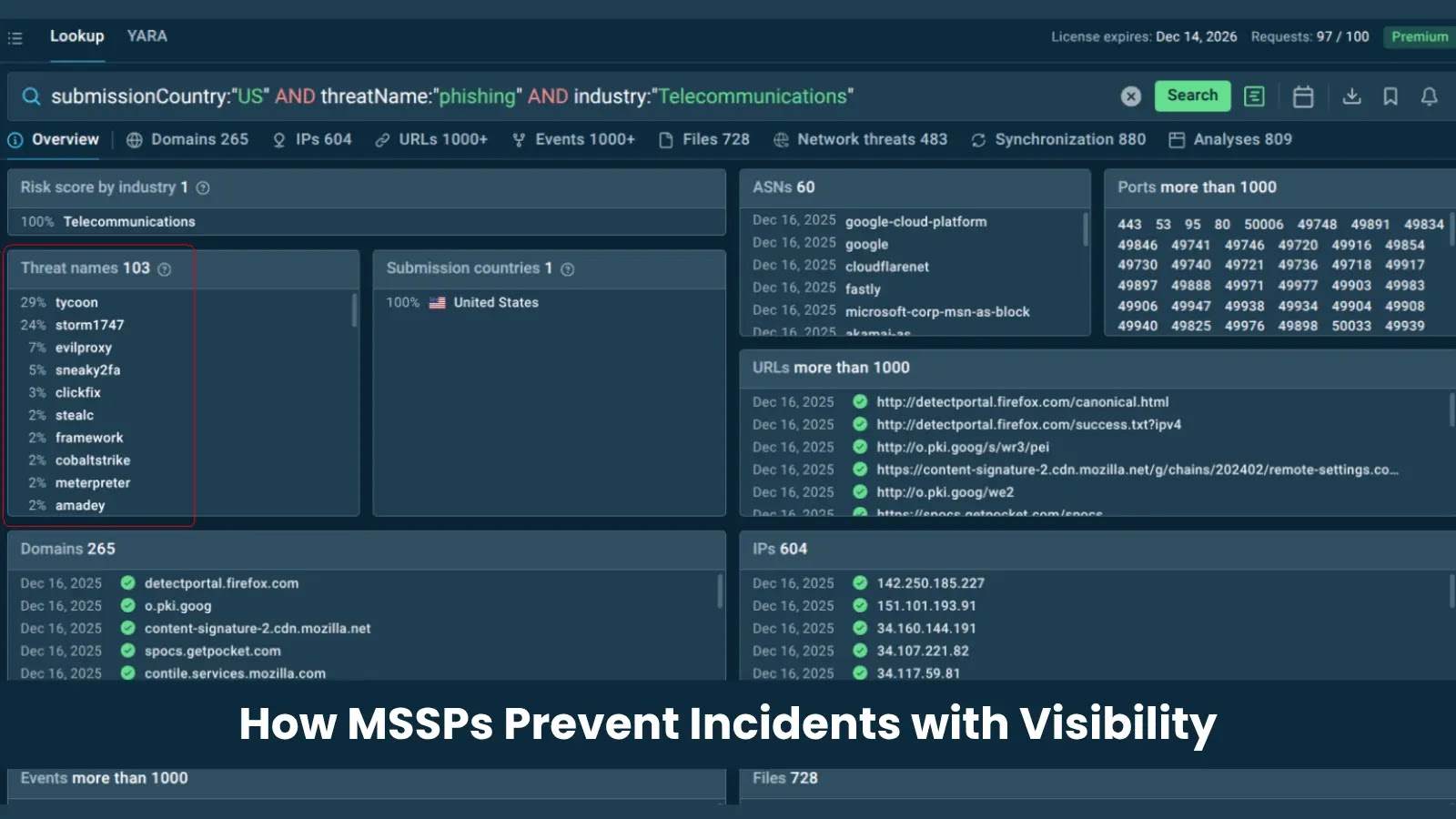
Beyond Basic Detection: The MSSP Advantage in Live Threat Visibility
Top-tier MSSPs move beyond rudimentary detection by implementing strategies that provide continuous, real-time insight into potential threats. They understand that a holistic view is paramount:
Unified Data Ingestion and Correlation
Leading MSSPs deploy sophisticated platforms that ingest data from every conceivable endpoint, network device, cloud service, and application. This isn’t just about collecting logs; it’s about normalizing, enriching, and correlating this data to build a comprehensive picture of activity. By integrating various data sources, they can identify subtle patterns that individual tools might miss. For instance, a single failed login attempt might be benign, but repeated failed logins from a new geographical location, coinciding with unusual outbound network traffic, points to a potential CVE-2022-26134 credential stuffing or brute-force attack.
Advanced Behavioral Analytics and AI/ML
Reliance on static, signature-based detection is insufficient in the face of modern threats. MSSPs leverage Artificial Intelligence (AI) and Machine Learning (ML) algorithms to establish baselines of normal behavior across their clients’ environments. Deviations from these baselines, even without known signatures, trigger alerts. This allows for the proactive identification of anomalous user behavior, insider threats, and sophisticated malware that might bypass traditional antivirus signatures. For example, an employee suddenly accessing unusual file shares or attempting to delete logs could indicate a malicious actor or a rogue insider.
Continuous Threat Hunting and Proactive Intelligence
Visibility is not passive. Elite MSSPs employ dedicated threat hunting teams that actively search for threats within client environments, rather than waiting for alerts. They utilize the latest threat intelligence feeds, including proprietary and closed-source information, to anticipate attacker tactics, techniques, and procedures (TTPs). This proactive approach helps them discover threats that have evaded automated detection systems, potentially uncovering previously unknown vulnerabilities like CVE-2023-38815 before they can be exploited.
Orchestration and Automated Response
Live threat visibility is only valuable if it leads to swift action. MSSPs integrate Security Orchestration, Automation, and Response (SOAR) platforms to automate repetitive tasks and accelerate incident response. When a high-fidelity threat is detected, automated playbooks can isolate affected endpoints, block malicious IP addresses, or trigger additional forensic data collection. This dramatically reduces the mean time to detect (MTTD) and mean time to respond (MTTR), minimizing the potential impact of an incident.
Remediation Actions: Practical Steps Towards Enhanced Visibility
For organizations looking to bolster their security posture, adopting principles of live threat visibility is crucial. Here are actionable steps:
- Consolidate and Centralize Logging: Implement a robust SIEM or Extended Detection and Response (XDR) solution to collect logs from all network devices, endpoints, applications, and cloud environments. Ensure proper parsing and normalization.
- Implement Behavioral Analytics: Beyond signature-based tools, deploy solutions that can establish baselines of normal behavior and flag deviations. This is critical for detecting zero-day attacks and insider threats.
- Integrate Diverse Threat Intelligence: Subscribe to and actively integrate multiple threat intelligence sources, including industry-specific feeds. Automate the ingestion and application of new IOCs into your detection rules.
- Perform Regular Vulnerability Assessments and Penetration Testing: Proactively identify security weaknesses that attackers might exploit. Address critical vulnerabilities like those outlined in CVE-2023-46805 and CVE-2024-21887 promptly.
- Develop and Practice Incident Response Plans: Visibility is incomplete without a clear plan for what happens next. Regularly rehearse incident response scenarios to ensure all team members understand their roles and responsibilities.
- Consider an MSSP Partner: For many organizations, achieving comprehensive live threat visibility internally is a significant undertaking. Partnering with a top-tier MSSP can provide access to specialized expertise, advanced tools, and 24/7 monitoring that would otherwise be cost-prohibitive.
Conclusion: The Imperative of Uninterrupted Sight
The digital landscape unforgivingly punishes even fleeting moments of invisibility. For top MSSPs, incident prevention is not a matter of luck but of comprehensive, uninterrupted sight. By unifying data, leveraging advanced analytics, employing proactive threat hunting, and automating responses, they eliminate blind spots and secure their clients against the sophisticated threats of today and tomorrow. The future of cybersecurity belongs to those who can truly “see” everything, all the time.