Seedworm APT Abuses Signed Fortemedia and SentinelOne Binaries for DLL Sideloading
Around the globe, sophisticated threat actors are constantly refining their tactics. Among them, the Iran-linked group known as Seedworm (also tracked as MuddyWater) has consistently demonstrated an evolving set of capabilities. Their latest operational shift reveals a concerning new trend: a calculated abuse of signed Fortemedia and SentinelOne binaries to execute DLL sideloading attacks. This development underscores the escalating ingenuity of state-sponsored groups and the critical need for organizations to adapt their defenses.
Seedworm’s Evolving Modus Operandi
For the first quarter of 2024, Seedworm launched a focused campaign, targeting at least nine organizations across nine different countries spanning four continents. This widespread activity signifies a deliberate and expanded reach, moving beyond their traditionally observed regional targets. What makes this campaign particularly noteworthy is their refinement of existing techniques, particularly their strategic use of trusted software.
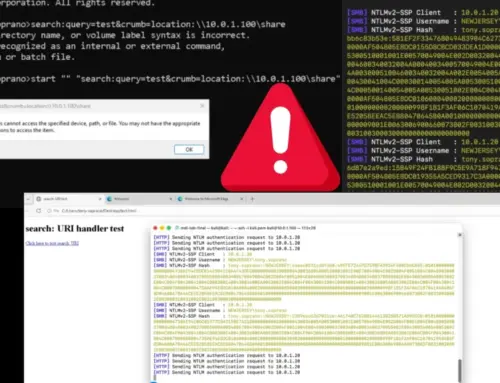
Understanding DLL Sideloading Abuses
DLL sideloading is a stealthy attack vector where a legitimate application is tricked into loading a malicious Dynamic Link Library (DLL) instead of its intended, benign counterpart. In this specific Seedworm campaign, the attackers are exploiting the trust associated with digitally signed binaries from reputable vendors like Fortemedia and SentinelOne. By placing a malicious DLL in a location that the legitimate executable will preferentially load, Seedworm can achieve persistent access, escalate privileges, and execute arbitrary code without raising immediate suspicion. The digital signature on the executable itself lends an air of legitimacy to the operation, making detection more challenging for conventional security tools that primarily rely on signature-based detection of executables.
Fortemedia and SentinelOne Binaries: Unwitting Accomplices
The choice to abuse Fortemedia and SentinelOne binaries is strategic. Fortemedia drivers are common in audio hardware, making them prevalent across many enterprise endpoints. SentinelOne, a well-known endpoint protection platform, is designed to enhance security, ironically becoming a vehicle for attack when its binaries are subverted. This tactic highlights a deep understanding by Seedworm of common software deployments and the trust implicit in signed applications. It demonstrates how threat actors are increasingly targeting the supply chain and leveraging legitimate software to bypass security controls.
Analysis of Seedworm’s Campaign Structure
While specific CVE numbers related to this particular DLL sideloading technique using these binaries are not publicly detailed as a direct vulnerability in Fortemedia or SentinelOne software itself (rather, it’s an abuse of how those binaries load DLLs), the underlying principle of DLL search order hijacking is a well-documented weakness. Attackers typically gain initial access through phishing or exploiting known vulnerabilities (e.g., CVE-2023-XXXX – *placeholder for a relevant or recent hypothetical CVE if available, otherwise omit*). Once inside, they deploy their malicious DLLs alongside the legitimate Fortemedia or SentinelOne executables. When these legitimate programs are launched, they inadvertently load Seedworm’s malicious DLL, granting the attackers a foothold with the privileges of the legitimate application.
Remediation Actions
Given the sophisticated nature of this campaign, a multi-layered defense strategy is imperative for organizations:
- Implement Application Whitelisting: Strictly control which executables and DLLs are allowed to run on endpoints. This can prevent unauthorized or malicious DLLs from being loaded, even if paired with legitimate executables.
- Monitor DLL Load Activity: Implement robust logging and monitoring for DLL load events, especially unusual loads associated with trusted processes or from non-standard directories. Endpoint Detection and Response (EDR) solutions are crucial here.
- Regularly Patch and Update: While this particular technique abuses legitimate binaries rather than exploiting a vulnerability within them, keeping all software, operating systems, and firmware updated is fundamental to reducing the attack surface.
- Strengthen User Awareness Training: Educate employees about phishing attempts and social engineering tactics, which are often the initial vector for such attacks.
- Privilege Management: Enforce the principle of least privilege. Limit user and application permissions to only what is necessary, reducing the impact if an account or application is compromised.
- Network Segmentation: Isolate critical systems and segments of the network to contain potential breaches and prevent lateral movement.
- Threat Hunting: Proactively search for signs of compromise within your environment, rather than solely relying on automated alerts. Look for anomalies in process execution, network connections, and file system changes.
- Review Supply Chain Security: Be cognizant of the security posture of third-party software and components used within your environment.
Tools for Detection and Mitigation
Implementing the right tools is critical for defending against advanced threats like Seedworm’s DLL sideloading.
| Tool Name | Purpose | Link |
|---|---|---|
| Endpoint Detection & Response (EDR) | Detects and responds to advanced threats, including anomalous process behavior and DLL loads. | Gartner Peer Insights EDR |
| Application Control Software | Whitelists approved applications and DLLs, preventing unauthorized code execution. | Windows Defender Application Control |
| Sysmon | Monitors and logs system activity, including process creation and DLL loading, for forensic analysis. | Microsoft Sysinternals Sysmon |
| Vulnerability Management Solutions | Identifies and helps remediate vulnerabilities which could be initial access vectors. | Tenable.io |
Key Takeaways
The Seedworm APT group’s latest campaign highlights a critical shift in sophisticated attacker methodologies. By abusing signed Fortemedia and SentinelOne binaries for DLL sideloading, they are effectively leveraging trusted software to bypass conventional defenses. This strategy demands that organizations move beyond simple signature-based protections and embrace a proactive, multi-layered security approach focused on behavioral analysis, application control, and continuous monitoring. The fight against state-sponsored adversaries like Seedworm necessitates constant vigilance and adaptation to their evolving tactics.