VLAN Hopping Attacks and How to Prevent Them.
Mitigating VLAN Hopping Attack: Best Practices for VLAN Security and How to Prevent Them
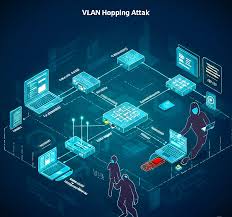
In today’s interconnected digital landscape, ensuring robust network security is paramount. Virtual Local Area Networks (VLANs) provide essential segmentation and isolation, yet they are not immune to sophisticated attacks. This article delves into the intricacies of VLAN hopping attacks, offering comprehensive insights and actionable strategies to fortify your network’s defenses.
Understanding VLAN Hopping Attacks
VLAN hopping attacks represent a significant threat to network infrastructure, potentially allowing attackers to bypass VLAN boundaries and gain unauthorized access to sensitive network segments. Understanding how these attacks work and the various types is crucial for implementing effective preventative measures. This section provides a detailed overview of VLAN hopping, equipping network administrators with the knowledge to mitigate these risks effectively.
Basics of VLAN
The basics of VLANs are essential to understanding network segmentation. A virtual local area network (VLAN) logically divides a physical network into multiple, separate broadcast domains. VLAN segmentation enhances network performance and security by isolating traffic within each VLAN. Each VLAN operates as its own virtual local area, improving manageability and reducing the risk of broadcast storms. A VLAN ID identifies each VLAN, and devices within the same VLAN can communicate directly, while communication between different VLANs requires routing.
How VLAN Hopping Works
A VLAN hopping attack allows the attacker to send traffic from one VLAN to another without proper authorization. VLAN trunking, typically using the 802.1q protocol, carries traffic for multiple VLANs over a single physical link. In a basic VLAN hopping attack, an attacker exploits vulnerabilities in the VLAN configuration to send packets tagged with the target VLAN’s VLAN tag, effectively bypassing VLAN boundaries. These attacks often target the native VLAN or default configurations to gain unauthorized access.
Types of VLAN Hopping Attacks
Here are two main types of VLAN hopping attacks, each with its own method of exploitation:
- Switch spoofing involves an attacker mimicking a switch using dynamic trunking protocol (DTP) to establish a trunk link with the victim switch. This allows the attacker to send and receive traffic on all VLANs allowed on the trunk.
- Double tagging involves inserting two VLAN tags into a packet. The first tag is for the attacker’s VLAN, and the second is for the target VLAN. The switch forwards the packet to the target VLAN after stripping the first VLAN tag, allowing the attacker to bypass VLAN security measures.
Types of VLANs and Their Security Implications
Types of VLAN
Understanding the different types of VLANs is crucial for designing a secure and efficient network. Static VLANs, the most common type, are port-based, assigning a VLAN ID to each switch port. Dynamic VLANs, on the other hand, use software to assign VLAN memberships based on MAC addresses or other criteria. The choice of VLAN type impacts VLAN segmentation, and thus, VLAN security. A properly configured VLAN architecture is essential to prevent VLAN hopping attacks. Different VLAN configurations also offer varying levels of protection against man-in-the-middle attacks and other exploits.
VLAN Security Considerations
Several VLAN security considerations are paramount in preventing VLAN hopping attacks. Implementing these measures can significantly reduce the risk of such attacks. Some key considerations include:
- Always change default VLAN configurations, especially VLAN 1, as attackers often target it.
- Disable dynamic trunking protocol (DTP) on ports that do not require trunking to prevent switch spoofing attacks.
- Properly configure VLAN trunking to only allow necessary VLANs on the trunk link.
- Regularly monitor and manage VLAN traffic to detect and mitigate any suspicious activities or hopping attempts.
Risk of VLAN Hopping
The risk of VLAN hopping should not be underestimated, as successful attacks can compromise entire networks. VLAN hopping attacks allow the attacker to bypass VLAN boundaries, gaining unauthorized access to sensitive resources on different VLANs. This can lead to data breaches, network downtime, and significant financial losses. Therefore, implementing robust VLAN security measures and preventing VLAN hopping attacks is essential for protecting your network infrastructure. Addressing these risks proactively is a cornerstone of effective cybersecurity.
Techniques Used in VLAN Hopping
Switch Spoofing
Switch spoofing is a type of VLAN hopping attack where an attacker mimics a legitimate switch to establish a trunk link with the victim switch. By exploiting dynamic trunking protocol (DTP), the attacker can negotiate a trunk connection, allowing them to send and receive traffic on all VLANs allowed on the trunk. To prevent switch spoofing attacks, it is critical to disable DTP on ports that do not require trunking. Proper VLAN configuration and monitoring are crucial in detecting and mitigating such attacks.
Double Tagging
Double tagging is another prevalent technique used in VLAN hopping attacks. In a double tagging attack, the attacker inserts two VLAN tags into a packet. The first VLAN tag is for the attacker’s VLAN, while the second VLAN tag is for the target VLAN. When the packet reaches the first switch, it strips the first VLAN tag and forwards the packet to the target VLAN based on the second VLAN tag, effectively bypassing VLAN boundaries. To prevent double tagging attacks, proper VLAN configuration and VLAN segmentation are essential, particularly in environments with an unused native VLAN.
Exploiting VLANs
Attackers can exploit VLAN vulnerabilities to perform VLAN hopping attacks and gain unauthorized access to sensitive network segments. To enhance VLAN security, it’s important to follow best practices, such as:
- Changing the default native VLAN.
- Disabling unused VLANs.
- Implementing strict VLAN access controls is vital to prevent switch spoofing and double tagging vulnerabilities.
Consistently monitor and manage VLAN configurations and VLAN traffic.
Best Practices to Prevent VLAN Hopping
Implementing VLAN Security Measures
Implementing robust VLAN security measures is crucial to prevent VLAN hopping attacks and maintaining network integrity. Begin by changing the default VLAN ID, specifically VLAN 1, as it is a common target for attackers. Ensure that all unused VLAN IDs are disabled to eliminate potential entry points. Regularly update switch firmware and security patches to mitigate known vulnerabilities. These foundational steps significantly reduce the risk of VLAN hopping and enhance overall network security.
Configuration Best Practices
Following configuration best practices is essential for a secure VLAN architecture. Disable dynamic trunking protocol (DTP) on ports that do not require trunking to prevent switch spoofing attacks. Explicitly configure VLAN trunking to only allow necessary VLANs on the trunk link. Set the native VLAN to an unused VLAN ID and ensure it is not used for any active devices. Proper VLAN configuration minimizes the opportunities for attackers to exploit vulnerabilities and bypass VLAN boundaries, thus preventing layer 2 attacks.
Regular Network Audits
Regular network audits are vital for identifying and addressing potential VLAN security vulnerabilities. Conduct periodic reviews of VLAN configurations to ensure adherence to best practices. Monitor VLAN traffic for any unusual patterns or hopping attempts that could indicate malicious activity. Vulnerability scans can help identify misconfigured VLANs and weaknesses that attackers can exploit. Network audits provide ongoing vigilance and contribute to a robust defense against VLAN attacks.
Mitigating VLAN Hopping Attacks
Strategies to Mitigate Risks
Developing effective strategies to mitigate risks is paramount in preventing VLAN hopping attacks. Implementing strict access control lists (ACLs) to filter traffic between VLANs can prevent unauthorized communication. Employ intrusion detection and prevention systems (IDPS) to monitor for and block malicious VLAN traffic. Regularly train network administrators on VLAN security best practices to ensure they can effectively manage and mitigate potential threats. These proactive measures significantly reduce the risk of VLAN attacks, including successful VLAN hopping.
Monitoring and Detection Techniques
Employing robust monitoring and detection techniques is essential for identifying VLAN hopping attempts in real-time. Implement network monitoring tools to analyze VLAN traffic patterns and detect anomalies. Configure alerts to notify administrators of suspicious activities, such as unexpected traffic between VLANs. Employ intrusion detection systems (IDS) to identify and log potential VLAN hopping attacks. Continuous monitoring and proactive detection are crucial for mitigating VLAN security risks effectively.
Responding to VLAN Attacks
Having a well-defined incident response plan is crucial for effectively responding to VLAN attacks, especially those involving switch spoofing and double tagging. Upon detecting a VLAN hopping attack, immediately isolate the affected VLAN to prevent further damage. Analyze the attack to identify the source and method used. Implement necessary security measures, such as patching vulnerabilities and reconfiguring VLANs, to prevent future attacks. Document the incident and lessons learned to improve future incident response. A swift and effective response minimizes the impact of VLAN security breaches.
How can I prevent VLAN hopping attacks and protect my virtual local area network?
Prevent VLAN hopping attacks by enforcing secure trunk configurations and removing the native untagged VLAN from trunks: set the native VLAN to an unused VLAN and ensure it is not carrying production traffic. Avoid using VLAN as the native untagged value for any trunk and explicitly tag VLAN traffic where possible. Disable dynamic trunking protocols, restrict which ports can be trunks, and apply port security and access control lists so unauthorized VLAN traffic is blocked. Regularly audit your VLAN device inventory and correct any incorrect VLAN assignments to reduce chances that a compromised VLAN or an unnecessary VLAN can be exploited to bypass VLAN segmentation.
What VLAN hopping techniques do attackers use and how do attacks occur?
VLAN hopping techniques commonly include switch spoofing and double tagging. In switch spoofing an attacker configures a device to appear as a switch and negotiate a trunk, allowing traffic to any VLAN. Double tagging involves crafting a packet with two VLAN tags so the outer tag is stripped by the first switch and the inner tag forwards the frame to the target VLAN id, enabling traffic to another VLAN. These VLAN-based attacks occur when trunks are misconfigured, when native VLAN of the trunk is left as default, or when untagged VLAN on the trunk carries sensitive traffic, allowing attackers to send packets through any VLAN or frame to all native VLAN ports.
Why do VLAN hopping attacks pose a serious risk to virtual local area networks?
VLAN hopping is a network security concern because it can allow attackers to bypass VLAN segmentation and access network resources of a VLAN they should not reach. If an attacker gains a foothold on an incorrect or compromised VLAN, they can use VLAN hopping techniques to reach an unauthorized VLAN and access services or sensitive data. The risk increases with default native VLAN settings, ports to an unused VLAN not applied, or a lack of proper VLAN device inventory and monitoring.
How can I configure ports and trunks to avoid VLAN hopping and prevent attacks occur?
To avoid VLAN hopping attacks occur, configure all trunk ports with an explicit native VLAN that is unused for user traffic, or better, tag the native VLAN where supported. Disable unused ports and assign them to a dedicated unused VLAN, and change the native VLAN of all trunk ports from defaults. Use VLAN access control lists, enable BPDU guard and disable auto trunking protocols to prevent a device from forming a trunk. Ensure the native VLAN of the trunk is consistent across switches so a packet with two VLAN tags cannot be misrouted between mismatched native VLANs.
What monitoring and policies help detect and stop VLAN-based attacks and known as VLAN hopping?
Deploy network monitoring and intrusion detection rules that look for anomalous patterns such as frames to all native VLAN or packets with two VLAN tags, and logs for unexpected trunk negotiations. Maintain a current VLAN device inventory and enforce policies that prevent devices from attempting to negotiate trunks. Regular vulnerability assessments and segmented access controls reduce the impact if a compromised VLAN is found. Together with strict configuration—no default native VLANs, disabling dynamic trunking, and limiting vlan on the trunk—these measures make VLAN hopping attacks much harder to execute.

![[Security Brief] - P15 - VLAN Hopping Attacks](https://lepuchin.com/uploads/images/image_750x_66afc77d370e8.jpg)





